Abstract
In this project, we examine how pervasive computing environments can leverage behavioral biometrics for identifying and authenticating users. The main challenge this project is addressing is the question how behavioral biometrics approaches scale to environments, containing multiple users with changing behavior, different physicalities, and changing sensing and interaction capabilities.
The problem with traditional authentication
Knowledge-based authentication mechanisms that require users to remember login and password are among the most popular means for authentication, despite the fact that they were never designed for today's requirements. For example password-based authentication originates in the mainframe era around 1960 where users would log onto a single device a few times a day at most. Today authentication happens much more frequently as well as in almost any situation and context. As a result, authentication creates a significant overhead (using state-of-the-art authentication mechanisms, people spend on average 90 minutes per month authenticating), which ultimately leads to many users using weak (but therefore faster) means to protect sensitive data or no protection at all.
Behavioural Biometrics as a promising alternative
In the past years, behavioral biometrics, that is the ability to identify users implicitly from their behavior, received considerable attention in the research community. This approach does not require users to remember a secret but authentication can seamlessly slide into the background without the need for active user engagement. Suitable behavioural traits to identify users include, but are not limited to, users’ gait, typing behavior, touch targeting behavior, gaze behavior, and mouse movements. At the same time, behavioral biometrics so far was mainly investigated in the lab for a single user at a time since assessing different features requires precise measurements in controlled environments. Thus it remains unclear how these approaches scale to the novel challenges of pervasive computing environments.
Research Questions
In this project we address this new field by answering questions like
- how users’ behavior is influenced both by people in the vicinity, characteristics of a space (either public or private), as well as by novel interaction techniques,
- how this influences the way in which we design and develop behavioral biometrics systems, and
- what this means for behavioral biometrics-based authentication concepts (e.g., how can we build user interfaces that foster a certain behavior; how can appropriate behavioral traits be identified based on the current context).
Impact
We envision this project to enable a significant leap forward towards behavioral biometrics becoming a powerful means for identification and authentication in future pervasive computing environments that combine high usability with strong security. Furthermore the outcomes of this project are valuable beyond security, e.g. the adaption of interfaces for individual users based on features like their body physique or current pose.
Publikationen
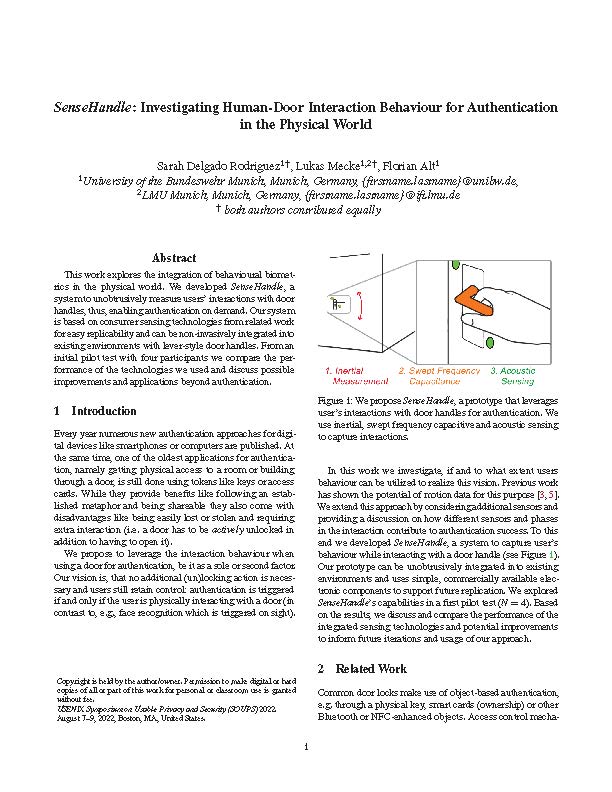 |
Sarah Delgado Rodriguez, Lukas Mecke und Florian Alt. SenseHandle: Investigating Human-Door Interaction Behaviour for Authentication in the Physical World. In Adjunct Proceedings of the Eighteenth Symposium on Usable Privacy and Security. SOUPS '22. USENIX Association, [Download Bibtex] | |
 |
Stefan Schneegass, Alia Saad, Roman Heger, Sarah Delgado Rodriguez, Romina Poguntke und Florian Alt. An Investigation of Shoulder Surfing Attacks on Touch-Based Unlock Events. In Proc. ACM Hum.-Comput. Interact., 6, [Download Bibtex] | |
 |
Yasmeen Abdrabou, Sheikh Radiah Rivu, Tarek Ammar, Jonathan Liebers, Alia Saad, Carina Liebers, Uwe Gruenefeld, Pascal Knierim, Mohamed Khamis, Ville Mäkelä, Stefan Schneegass und Florian Alt. Understanding Shoulder Surfer Behavior and Attack Patterns Using Virtual Reality. In Proceedings of the International Conference on Advanced Visual Interfaces. AVI '22. Association for Computing Machinery, New York, NY, USA. [Download Bibtex] | |
 |
Florian Alt und Stefan Schneegass. Beyond Passwords—Challenges and Opportunities of Future Authentication. [Download Bibtex] | |
 |
Saad Alia, Izadi Kian, Ahmad Khan Anam, Knierim Pascal, Schneegass Stefan, Alt Florian und Abdelrahman Yomna. HotFoot: Foot-Based User Identification Using Thermal Imaging. In Proceedings of the 2023 CHI Conference on Human Factors in Computing Systems. CHI '23. Association for Computing Machinery, New York, NY, USA. [Download Bibtex] | |
 |
Jonathan Liebers, Uwe Gruenefeld, Lukas Mecke, Alia Saad, Jonas Auda, Florian Alt, Mark Abdelaziz und Stefan Schneegass. Understanding User Identification in Virtual Reality through Behavioral Biometrics and the Effect of Body Normalization. In Proceedings of the 2021 CHI Conference on Human Factors in Computing Systems. CHI'21. Association for Computing Machinery, New York, NY, USA. [Download Bibtex] | |
 |
Ken Pfeuffer, Matthias Geiger, Sarah Prange, Lukas Mecke, Daniel Buschek und Florian Alt. Behavioural Biometrics in VR - Identifying People from Body Motion and Relations in Virtual Reality. In Proceedings of the 2019 CHI Conference on Human Factors in Computing Systems. CHI '19. ACM, New York, NY, USA. [Download Bibtex] | |
 |
Lukas Mecke, Sarah Delgado Rodriguez, Daniel Buschek, Sarah Prange und Florian Alt. Communicating Device Confidence Level and Upcoming Re-Authentications in Continuous Authentication Systems on Mobile Devices. In Fifteenth Symposium on Usable Privacy and Security (SOUPS 2019). USENIX Association, Santa Clara, CA. [Download Bibtex] [Video] | |
 |
Lukas Mecke, Daniel Buschek, Mathias Kiermeier, Sarah Prange und Florian Alt. Exploring Intentional Behaviour Modifications for Password Typing on Mobile Touchscreen Devices. In Fifteenth Symposium on Usable Privacy and Security (SOUPS 2019). USENIX Association, Santa Clara, CA. [Download Bibtex] [Video] | |
 |
Sarah Prange, Lukas Mecke, Alice Nguyen, Mohamed Khamis und Florian Alt. Don't Use Fingerprint, it's Raining! How People Use and Perceive Context-Aware Selection of Mobile Authentication. In Proceedings of the 2020 International Conference on Advanced Visual Interfaces. AVI'20. Association for Computing Machinery, New York, NY, USA. [Download Bibtex] |