Future IoT ecosystems demand secure, privacy-aware multi-domain operation (MDO) across heterogeneous networks and stakeholders.
Since the late 1970s, when interconnected research networks laid the foundation for today's Internet, the primary goals were knowledge exchange and shared computational resources across institutional boundaries. Over the decades, affordable devices, ubiquitous connectivity, and large-scale digital infrastructures have driven a paradigm shift toward the Internet of Things (IoT), where billions of heterogeneous devices continuously communicate across domains. While foundational Internet technologies remain in use, they require substantial adaptation to meet emerging communication patterns, dynamic trust relationships, and stringent privacy expectations. As digitalization, automation, and continuous connectivity expand, privacy has become a core societal concern: the ability to control information disclosure directly influences liberty, innovation, and trust in digital ecosystems. Consequently, modern solutions must provide adaptable, reusable, and stakeholder-centric mechanisms for security, privacy, and trust—particularly in complex MDO scenarios.
Today, individuals commonly operate several IoT-enabled devices-ranging from smartphones and wearables to access credentials and smart infrastructure components. These devices differ in resources, communication technologies, timing constraints, and security capabilities. They interact through diverse communication patterns, including Human-to-Machine (H2M) and Machine-to-Human (M2H), Machine-to-Data-Lake (M2D) and Machine-to-Analytics (M2A), as well as Machine-to-Process (M2P) and Machine-to-Machine (M2M). In multi-domain environments - where devices, services, and stakeholders span organizational, administrative, and regulatory boundaries - these interaction patterns significantly increase complexity. Trust establishment, identity management, access control, policy enforcement, and secure data lifecycle management must function seamlessly across domains without sacrificing autonomy or compliance.
Thus, SeCoSys - Secure Communication Systems - addresses these challenges by investigating secure air/ground communications and broader IoT infrastructures under a unified multi-domain perspective. The work is structured along two interdependent pillars: Communication Networks and Data Management. The first pillar (blue) focuses on resilient architectures, secure transmission protocols, authentication and key management mechanisms, and cross-domain interoperability. The second pillar (orange) addresses privacy-aware data handling, access governance, secure storage, analytics integration, and compliance with evolving legal frameworks. Both pillars are systematically structured and interconnected through a set of overarching horizontal services, where these cross-cutting layers span all architectural components and ensure consistent operation across domains:
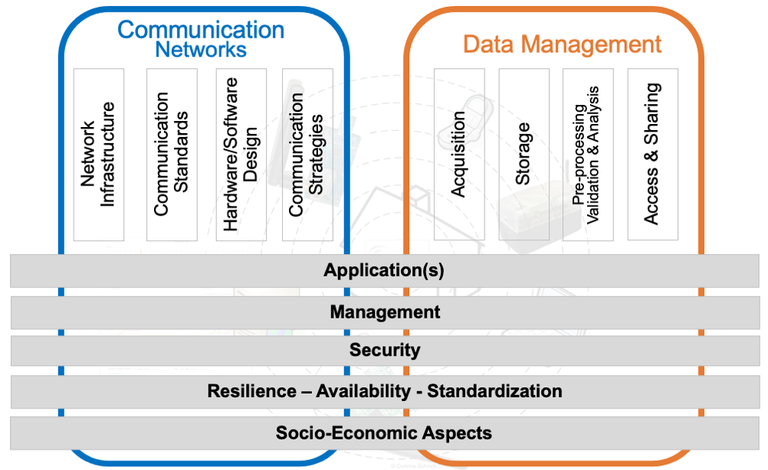
- Applications provide the functional integration of network and data capabilities into domain-specific use cases.
- Management enables orchestration, configuration, monitoring, and lifecycle control of distributed systems.
- Security establishes identity and trust management, access control, and protection mechanisms for communication and data handling.
- Resilience, availability, and standardization ensure interoperability, robustness, and continuity of operations across heterogeneous and federated environments.
- Socio-economic analysis evaluates regulatory compliance, stakeholder requirements, risk, and sustainability aspects.
Together, these horizontal services ensure that security, privacy, trust, and operational consistency are enforced coherently across both pillars and throughout complex multi-domain ecosystems.
This currently results in three research areas for SeCoSys, which form corresponding synergies in the field of "multi-domain operations (MDO):
Photos: © SeCoSys/Schmitt