CODE Capture the Flag 2019 „The 5th Element – It mu5t be found“
22 November 2019
2019 is the year when worlds collide. It was the pleasure of RI CODE, ITIS e.V., and Team localos to fight together with the participating teams against the darkness during the Capture the Flag (CTF) 2019
The fifth CTF started on 22nd November 18:00 at the Bundeswehr University Munich (BUM) and lasted 18 hours until 23 November 12:00. Over 120 participants grouped in 29 teams were eager to fight against the darkness and win honor and glory and thereby the five elements. Also several students teams and teams from the CONCORDIA consortium participated in the CTF.

Participant trying to solve a challenge at the CTF
CTFs in computer security are a type of computer security competitions. The contests are usually designed to serve as an educational exercise. CTFs help to support the training Cybersecurity professionals. That’s the reason CODE CTFs were established in the first place. During CTFs students can test and practice their theoretical knowledge in different practical challenges. Therefore, CTFs are a great way to learn a wide array of computer security skills in a safe, legal, and fun environment.
There are different styles: attack/defence, Jeopardy, and hybrid. The teams attempt to earn the most points by solving tasks in a certain time frame. While some events have fixed points per challenge dependent on the level of difficulty - especially in Jeopardy - our CTF used a unique dynamic scoring. Dynamic scoring can lead to strategic decisions, e.g., which challenge to solve next either to gain more points or let other teams reduce their points.

Only one team solved the hardest hardware challenge
In order to participate, the teams had to go through an online qualifying first, where they could earn up to seven flags and one easteregg. 29 teams with four team members each at the maximum got qualified for the on-site main event. The Jeopardy-style CTF involved multiple categories of challenges, like crypto, web, forensic, and reverse/pwn, for which the teams had a limit of 18 hours to solve. Besides typical challenges mostly based on real exploits, several extraordinary challenges were available. For example a hardware challenges involving an oscilloscope, a sort of geo caching challenge with Bluetooth beacons, and even a VR challenge (see image below) by Team localos were challenging the participants. Of course, catering and support was provided to the participants for free.

VR Challenge
The event ended with credits in a small movie and an award ceremony, where the best professional teams and students teams were awarded. Congratulations to the winners!

Award ceremony
Best professional teams:
- [✓] T6 (Also the only team solving the hardest hardware challenge)
- 0x90
- call_0x9011111
- tronicorn
- Blue Eagle
- Pink Fluffy Unicorn
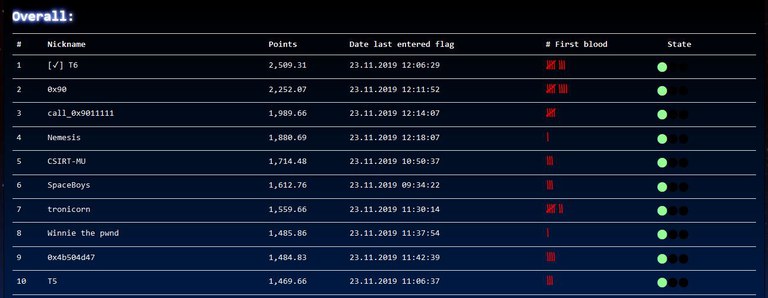
Final Scoreboard
Have you missed it? Interested in playing the next CTF? Further information are available at https://ctf.code.unibw-muenchen.de and hopefully see you next year.
Logo: © Team localos